Adding intelligence to labels – barcodes, RFID and beyond
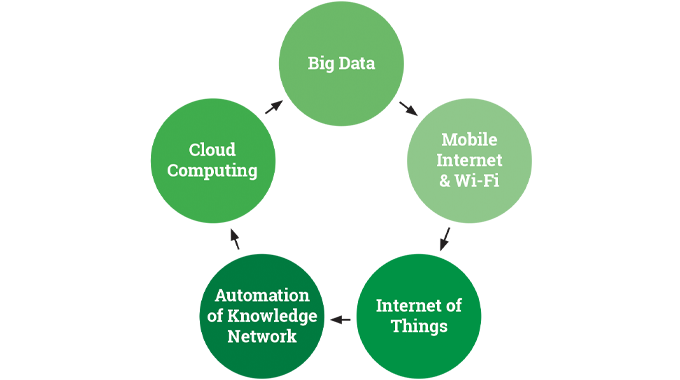
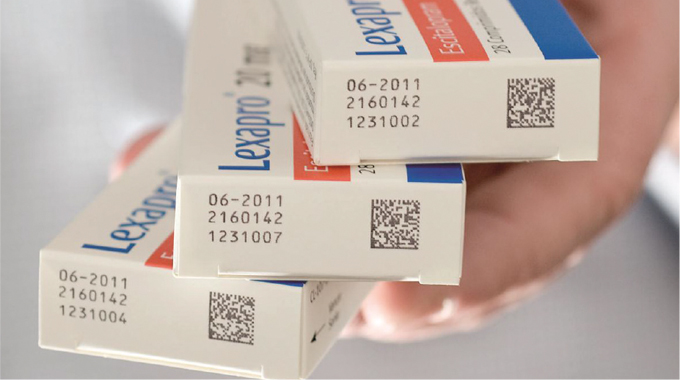
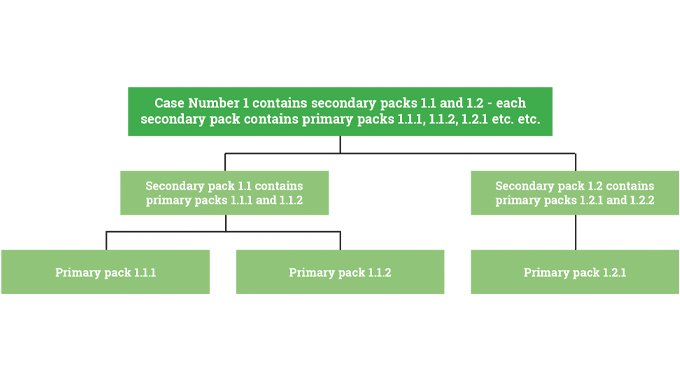
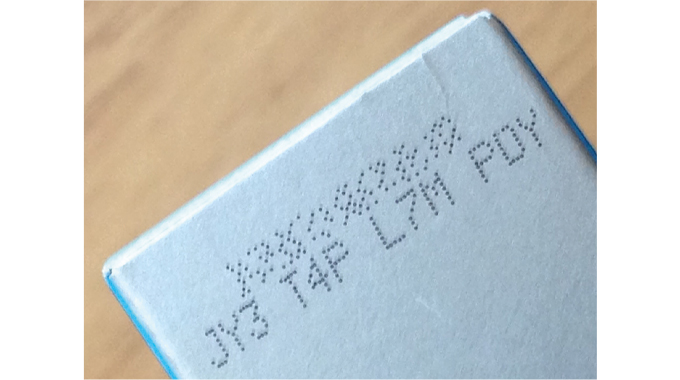
The word ‘intelligence’, often used as a prefix to labels and also packaging, is rather a misnomer since true intelligence requires thought, analysis and intellectual processing. However, intelligent labels and smart packaging are terms we all recognize and associate with systems and devices on packaging that are designed to deliver valuable additional product information to us at point of purchase or point of use.
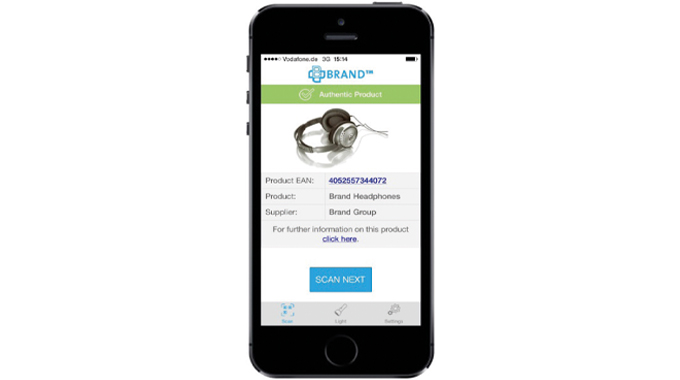
This additional useful information may be acquired visually as a color change indicator for instance, or for more complex information exchange the use of a smart phone may be required.
Stay up to date
Subscribe to the free Label News newsletter and receive the latest content every week. We'll never share your email address.