Building the foundations – origination
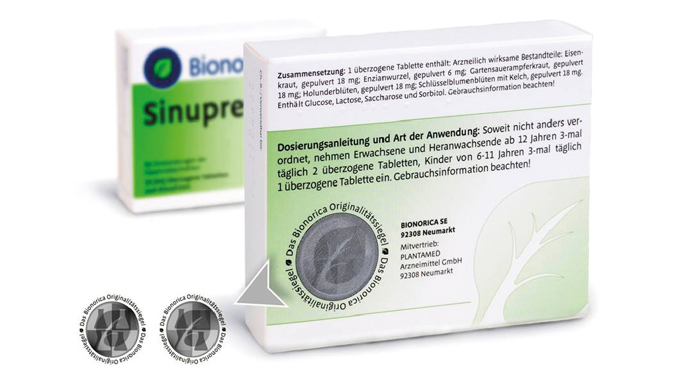
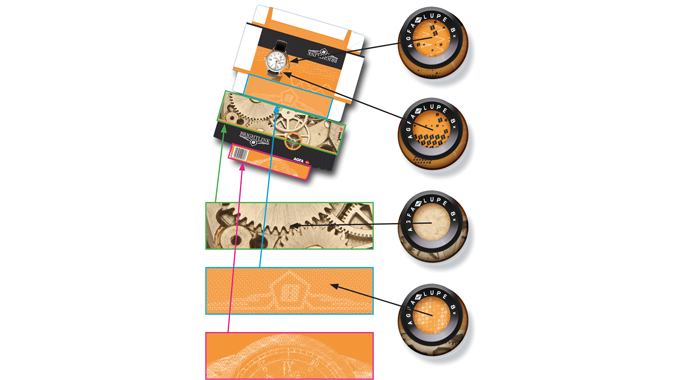
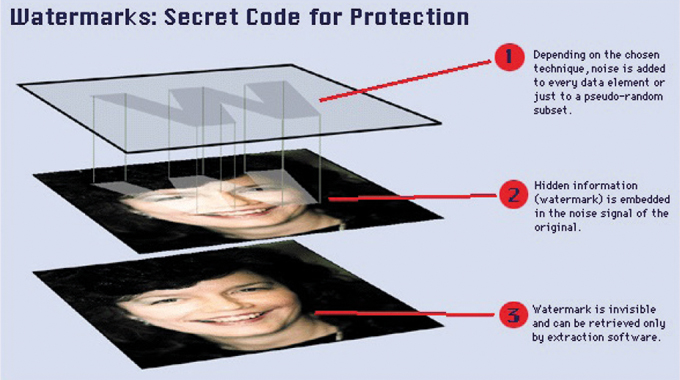
Every one of us is familiar with the functionality of security print design since we come into contact with banknotes and other high security print items on a regular basis. In the arena of labels and packaging however, security design is a relatively new concept to most suppliers in this field, as they are more familiar with designing for physical product protection, together with other functional requirements such as maximum brand recognition and the conveyance of useful information regarding product usage and ingredients.
As has been explained before, labels and packaging provide an ideal platform for the carriage of indicators of provenance as well as tamper evidence and track & trace technology.
Stay up to date
Subscribe to the free Label News newsletter and receive the latest content every week. We'll never share your email address.