Managing security issues as they affect products in the print business
The challenges relating to product security have always been present. From the earliest of times there has been a need to protect products from copying, dilution and tampering.
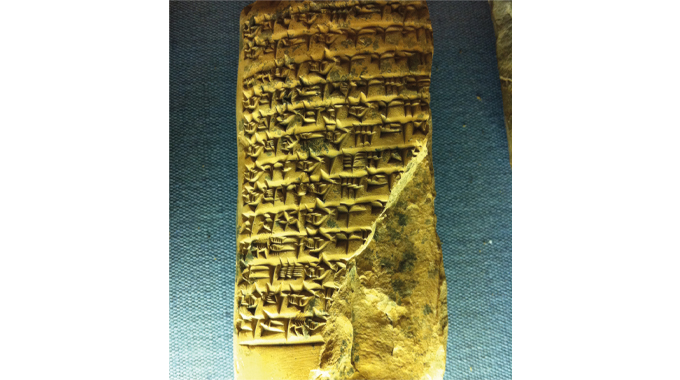
For instance, the Sumerians developed a very early form of labeling using clay tablets that carried the instructions for product use of goods that were stored and traded in baskets and amphorae (clay jars). By passing a piece of thin rope through the clay tablet they were able to create a basic form of tamper protection and guard against pilfering and copy attacks since each ‘label’ was individually crafted, fixed to the sealed closure (which was wax) and this acted as an early form of branding and quality assurance.
Stay up to date
Subscribe to the free Label News newsletter and receive the latest content every week. We'll never share your email address.